Introduction to CMMC Scoping
In today’s evolving cybersecurity landscape, compliance frameworks like the Cybersecurity Maturity Model Certification (CMMC) are essential for organizations contracting with the U.S. Department of Defense (DoD). CMMC aims to ensure that defense contractors and subcontractors effectively protect sensitive information through rigorous cybersecurity controls.
One of the initial and most crucial steps in achieving CMMC compliance is accurate CMMC scoping. Proper scoping can streamline your compliance journey, optimize your cybersecurity posture, and help avoid costly pitfalls.
In this guide, you’ll learn what CMMC scoping involves, how to distinguish between CMMC Levels 1 and 2, the differences between an organization-wide and an enclave approach, step-by-step methods for effective scoping, common mistakes to avoid, and best practices for continuous compliance.
What is CMMC Scoping, and Why Does It Matter?
CMMC scoping defines the boundary around systems, networks, assets, and processes that must comply with CMMC standards. Clearly defining this boundary is critical, as it directly impacts the scope and cost of assessments and the effectiveness of security controls.
Benefits of Accurate Scoping
- Cost Savings: Properly defined scopes reduce unnecessary expenditure on compliance and infrastructure.
- Efficient Compliance: Clear boundaries streamline audits and accelerate certification processes.
- Security Improvements: Precisely identified assets allow targeted and effective security controls.
Understanding CMMC Levels: Level 1 vs. Level 2
CMMC comprises multiple maturity levels, primarily Level 1 (Foundational) and Level 2 (Advanced).
Level 1 (Foundational)
Encompasses the basic safeguarding requirements for FCI specified in FAR Clause 52.204-21. All contractors in Level 1 must implement 17 basic cybersecurity practices to safeguard FCI.
- Applies to organizations handling only Federal Contract Information (FCI).
- Basic cybersecurity practices to safeguard information.
Example Scenario
- A subcontractor performing administrative tasks without handling Controlled Unclassified Information (CUI) requires only Level 1 compliance.
Level 2 (Advanced)
Encompasses the security requirements for CUI, as specified in NIST SP 800-171 Rev 2, per DFARS Clause 252.204-7012 [3, 4, 5]. This applies to contractors handling CUI, CTI, ITAR, or export-controlled data that is classified under CUI.
- Required for organizations storing, processing, or transmitting CUI.
- More stringent security practices aligning with NIST SP 800-171.
Example Scenario
- A manufacturing company producing parts for a DoD contract, directly managing CUI documentation, must meet Level 2 standards.
Organization-Wide vs. Enclave Approach
Determining your scope often means choosing between an organization-wide or an enclave approach. Understanding the differences is key to selecting the right fit for your organization’s needs and resources.
Organization-Wide Approach
An organization-wide approach applies CMMC compliance standards across all systems, networks, and processes within the entire organization. This means every aspect of your IT infrastructure, including both administrative and operational departments, must adhere to the required cybersecurity controls.
Pros
- Simplifies compliance management.
- Broad cybersecurity improvements across the organization.
Cons
- Potentially higher costs.
- Increased complexity.
Enclave Approach
An enclave approach isolates compliance efforts to a clearly defined subset or “enclave” within the organization. Only the specific systems, processes, and personnel directly involved with handling sensitive information (such as Controlled Unclassified Information or Federal Contract Information) must meet CMMC requirements. All other systems remain outside the compliance scope.
Pros
- Lower costs due to reduced compliance boundaries.
- Easier to manage focused security controls.
Cons
- Requires strict isolation and boundary maintenance.
- Risk of inadequate isolation leading to scope creep.
When to Choose Which
- Organization-Wide: Ideal if your organization frequently interacts with CUI across multiple departments.
- Enclave: Suitable for organizations with clearly defined, isolated processes managing sensitive data.
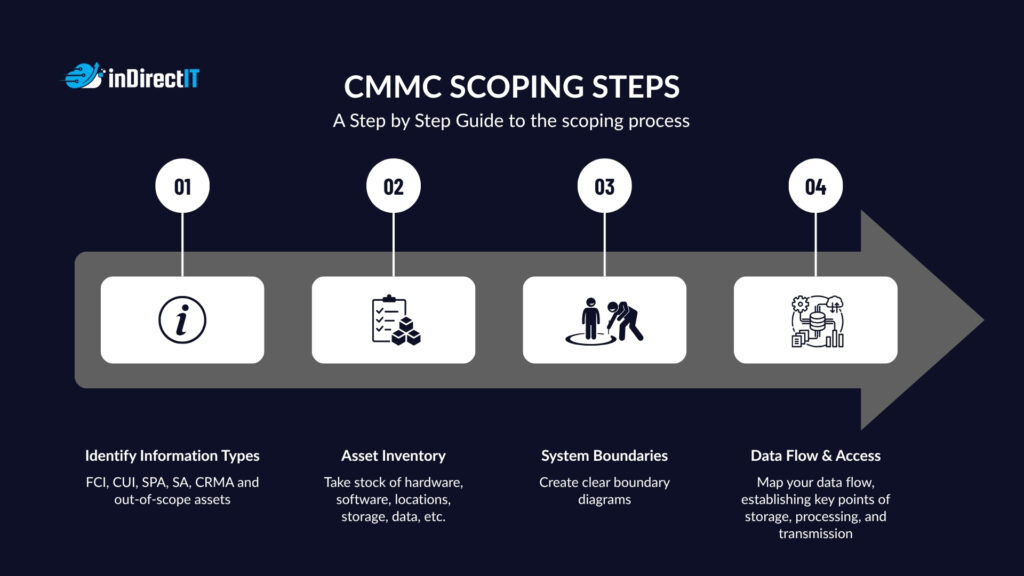
Step-by-Step Guide to Effective CMMC Scoping
1. Identify Your Information Types
Categorize your assets based on their sensitivity:
- Controlled Unclassified Information (CUI)
- Federal Contract Information (FCI)
- Security protection assets
- Specialized assets
- Contractor risk managed assets
- Out-of-scope assets
2. Asset Inventory
A comprehensive asset inventory includes:
- Hardware and software assets
- Physical locations
- Cloud services and storage solutions
- Data repositories
3. Define System Boundaries
Create clear boundary diagrams:
- Identify connections between internal and external systems.
- Clearly demarcate environments handling sensitive data.
- Document interconnections and dependencies.
4. Determine Data Flow and Access Controls
Map data flow comprehensively:
- Track how CUI and FCI move through your organization.
- Identify all points of data storage, processing, and transmission.
- Establish and document access control policies and procedures.
Common CMMC Scoping Mistakes
Mistake 1: Overly Broad or Narrow Scopes
- Pitfall: Including too many or too few systems, resulting in either unnecessary complexity or overlooked vulnerabilities.
- Solution: Regularly review your data flows and reassess scope boundaries to ensure accuracy.
Mistake 2: Misclassification of Assets
- Pitfall: Including too many or too few systems, resulting in either unnecessary complexity or overlooked vulnerabilities.
- Solution: Conduct thorough training on CUI handling and classification guidelines.
Mistake 3: Lack of Clear Boundary Definitions
- Pitfall: Including too many or too few systems, resulting in either unnecessary complexity or overlooked vulnerabilities.
- Solution: Use visual boundary diagrams and clear, descriptive documentation for scope clarity.
Mistake 4: Neglecting Third-Party Vendors and External Connections
- Pitfall: Including too many or too few systems, resulting in either unnecessary complexity or overlooked vulnerabilities.
- Solution: Include third-party service providers and external systems in your scoping assessments.
Best Practices for Continuous Compliance
Maintaining continuous compliance requires:
- Regular Scope Validation: Frequently revisit and adjust your scoping boundaries as your organization evolves.
- Accurate Documentation: Keep detailed records of asset inventories, boundary definitions, and control implementations.
- Periodic Reviews: Conduct routine assessments to ensure compliance and promptly address any changes in your infrastructure or data handling processes.
How inDirect IT Can Support Your CMMC Scoping Journey
Navigating the complexities of CMMC scoping can be challenging. inDirect IT offers specialized services tailored to help your organization:
- Gap Assessments: Identify gaps in your existing compliance and cybersecurity posture.
- Scoping Workshops: Expert-led workshops to clearly define your CMMC scope, tailored specifically to your organization’s needs.
- CMMC Enclave Solution: Establish a secure, compliant environment for your sensitive data.
Contact us today for a personalized consultation or detailed assessment of your current compliance landscape.
Conclusion
Accurate CMMC scoping is essential to achieving compliance efficiently and effectively. Through careful planning, clear definitions, and ongoing diligence, your organization can confidently meet its cybersecurity obligations. Implementing best practices, avoiding common pitfalls, and seeking expert guidance can significantly ease your compliance journey.
We encourage you to share this expert guide with your colleagues and peers to enhance collective awareness and preparedness in the evolving landscape of cybersecurity compliance.

Contact us today for a personalized consultation, comprehensive assessment, or detailed evaluation tailored specifically to your organization’s current compliance landscape.